PKI Career Pathway Cohort
A six-month, structured cohort guiding professionals through the full Public Key Infrastructure lifecycle—from foundational trust concepts to enterprise-grade engineering and architecture.
The PKI Career Pathway Cohort is an immersive, guided program designed for professionals seeking deep technical specialization in Public Key Infrastructure. Rather than isolated courses or self-paced content, this cohort delivers a cohesive learning experience that builds capability progressively across real-world PKI environments.
Participants move through three intentional phases—Foundations, Operations, and Engineering & Architecture—developing both technical depth and contextual understanding.
This progression prepares participants to support, design, and govern PKI in modern enterprise environments.
Program at a Glance
Duration: 6 months
Focus: Public Key Infrastructure (PKI)
Structure: Guided cohort delivered across three progressive phases
Format: Instructor-led sessions, hands-on labs, and applied enterprise scenarios
This is a single, continuous program—not standalone courses.
Pricing, payment options, and FAQs are available on the enrollment page.
A Single, Progressive Program
How the PKI Career Pathway Cohort Works
A structured progression designed to build capability, confidence, and real-world PKI readiness over six months.

This cohort is delivered as one continuous learning experience—not separate courses or disconnected modules. Each phase builds on the last, allowing participants to deepen technical understanding while applying concepts in increasingly complex enterprise scenarios.
Participants advance through three intentional phases, moving from foundational PKI concepts to operational execution and finally into engineering and architecture-level decision making.
Three Phases, One Cohesive Journey
Rather than choosing a starting point, participants are guided through the full PKI lifecycle in sequence—ensuring both depth and context at every stage.
The structure emphasizes:
Technical progression
Real-world applicability
Long-term role alignment in PKI-focused security careers
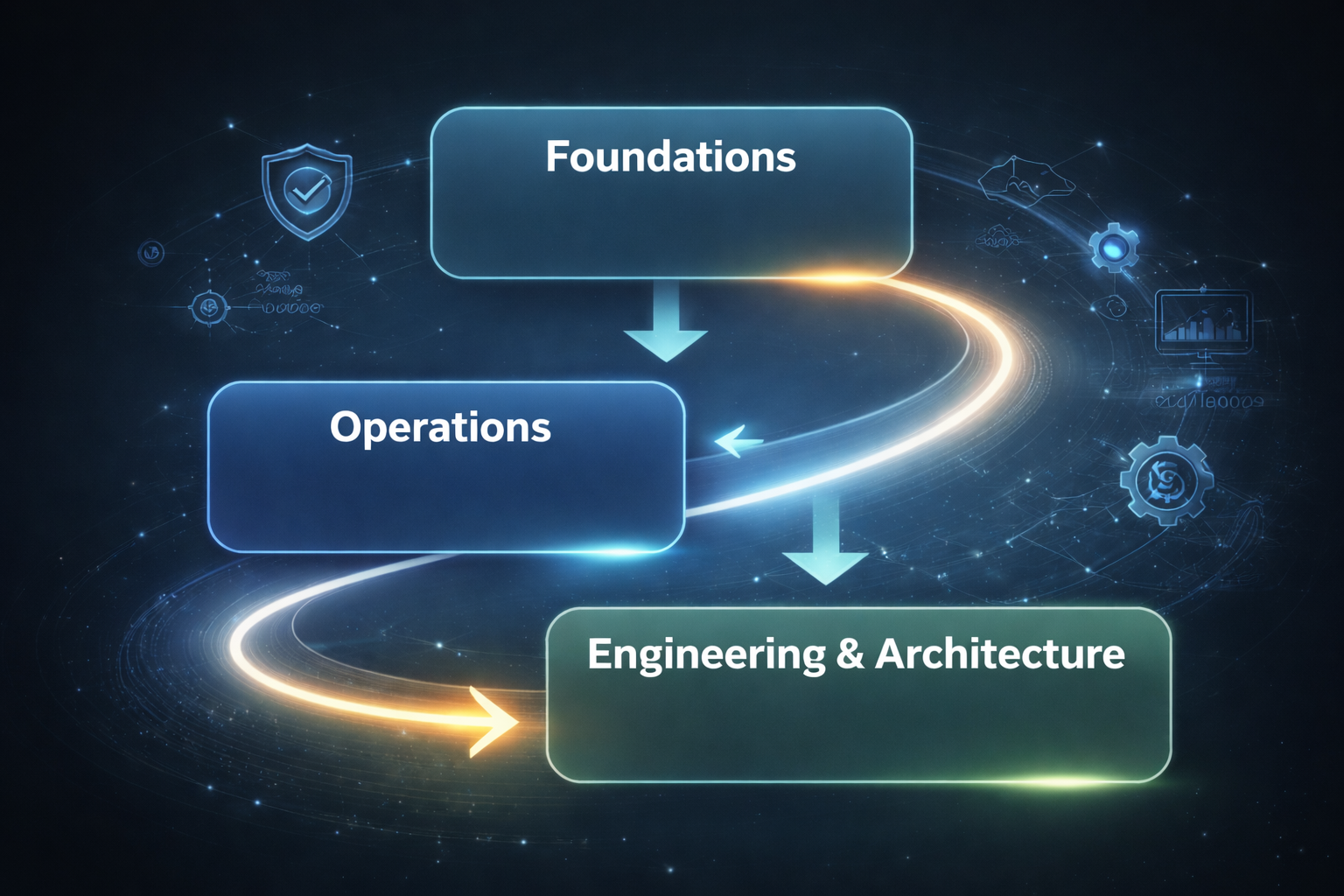
Foundations
PKI fundamentals, trust models, certificate lifecycles, and core concepts
Outcome: Build conceptual clarity and PKI literacy
Operations
Day-to-day PKI management, issuance workflows, monitoring, and incident considerations
Outcome: Operate PKI safely in live environments
Engineering & Architecture
Designing, scaling, and governing PKI in enterprise environments
Outcome: Design and evaluate PKI architectures with confidence
Three Phases. One Cohesive PKI Journey.
Each phase builds intentionally on the last, guiding participants from PKI fundamentals to enterprise-scale engineering and architecture.
This is not three separate courses — it is a single, progressive PKI program designed to mirror how PKI careers actually develop in the real world.

Phase 1: PKI Foundations
Positioning: Learn PKI without breaking production
Duration: 6–8 weeks
What This Phase Covers
This phase establishes the technical baseline required to work safely and confidently with certificates and trust systems. It focuses on conceptual clarity and real-world certificate literacy, without assuming administrative ownership of PKI infrastructure.
Key Focus Areas
PKI principles and trust models
Cryptography essentials (keys, hashing, signatures)
X.509 certificates and trust chains
TLS fundamentals and validation behavior
Hands-On Experience
Participants complete guided labs that include:
Generating keys and CSRs
Issuing and installing certificates
Validating certificate chains
Troubleshooting common TLS errors
Outcome
By the end of this phase, participants can:
Clearly explain how PKI works
Read and interpret certificates with confidence
Avoid common PKI misconfigurations
Phase 2: PKI Operations
Positioning: Operate PKI without outages
Duration: 6–8 weeks
What This Phase Covers
This phase moves from understanding PKI to owning its day-to-day operation. Participants learn how PKI behaves in production environments and how to manage it reliably at scale.
Key Focus Areas
PKI architecture and trust boundaries
Active Directory Certificate Services (AD CS)
Certificate lifecycle management
Revocation, monitoring, and expiration prevention
Hands-On Experience
Participants complete labs such as:
Building a two-tier CA hierarchy
Configuring templates and enrollment flows
Publishing and validating CRLs and OCSP
Recovering from PKI misconfigurations
Outcome
By the end of this phase, participants can:
Support enterprise PKI environments
Prevent certificate-related outages
Manage PKI operational workflows with confidence

Phase 3: PKI Engineering & Architecture
Positioning: Design PKI as critical infrastructure
Duration: 6–8 weeks
What This Phase Covers
The final phase focuses on enterprise-grade PKI design, automation, and resilience. Participants operate at an architectural level, making decisions that impact security, scalability, and continuity.
Key Focus Areas
Multi-tier PKI design and trust segmentation
Key protection strategies and HSM integration
Certificate lifecycle automation and CI/CD integration
Incident response and Zero Trust alignment
Hands-On Experience
Participants complete advanced labs including:
Integrating virtual or physical HSMs
Automating certificate issuance and renewal
Simulating large-scale PKI failures
Designing an enterprise PKI architecture
Outcome
By the end of this phase, participants can:
Architect and modernize enterprise PKI
Lead PKI initiatives and incident response
Act as PKI subject-matter experts within security teams
Pricing, payment options, and FAQs are available on the enrollment page.
What This Program Prepares You For
PKI Technical Fluency
Understand and explain PKI systems with confidence across enterprise environments.
Operational Readiness
Support, manage, and troubleshoot live PKI systems without causing outages.
Architectural Thinking
Design scalable, secure PKI aligned with enterprise architectures and Zero Trust models.
Career Alignment
Know where PKI fits in your role and how to grow into advanced positions.
Roles This Program Aligns You For
This cohort is designed to mirror how PKI responsibilities evolve in real enterprise environments. Participants graduate prepared to support, operate, and design PKI systems in roles that span engineering, operations, and security architecture.
PKI / Security Engineer
Primary alignment
Supporting and maintaining enterprise PKI environments
Managing certificate issuance, renewal, and revocation
Troubleshooting trust failures and certificate-related outages
Working with identity, infrastructure, and security teams
Identity & Access Management (IAM) Engineer
Contextual alignment
Understanding PKI as a foundational trust mechanism
Supporting authentication, device identity, and service trust
Working with certificates across identity workflows
Contributing PKI expertise within IAM and Zero Trust initiatives
Infrastructure or Platform Engineer (PKI-Focused)
Strong alignment
Integrating PKI into enterprise systems and platforms
Supporting TLS, authentication, and secure communications
Implementing automation for certificate lifecycle management
Collaborating with cloud, DevOps, and identity teams
Security Operations / Engineering Roles
Operational alignment
Monitoring certificate health and expiration risks
Preventing PKI-related incidents and outages
Supporting incident response tied to trust failures
Operating PKI safely in production environments
PKI Architect / Senior Engineer (Growth Path)
Advanced progression
Designing multi-tier PKI architectures
Making decisions around trust models, scale, and resilience
Aligning PKI with enterprise security and Zero Trust strategies
Serving as a PKI subject-matter expert within security teams
This program is not designed for a single job title — it prepares participants to grow into PKI-focused roles as their responsibilities expand.
Who This Program Is Designed For
This cohort is built for professionals who want to build real PKI capability, not just learn concepts. It is structured, technical, and requires active participation throughout the six-month journey.
This Program Is a Strong Fit If…
You are early-career or transitioning into cybersecurity and want deep, practical PKI experience
You already work in IT, infrastructure, security, cloud, or IAM and want to specialize
You want to understand how PKI works in real enterprise environments, not just theory
You are comfortable learning technical concepts over time and building progressively
You want a guided pathway with structure, accountability, and applied labs
You are interested in roles involving trust systems, identity, encryption, or secure communications
This program assumes curiosity, consistency, and a willingness to work through complexity.
This Program Is Not a Fit If…
You are looking for a quick certification or crash course
You want self-paced, passive video content only
You are not interested in hands-on labs or applied technical work
You are seeking a non-technical cybersecurity overview
You are not able to commit consistent time over a six-month period
You want guaranteed job placement rather than skill and readiness development
This cohort mirrors real PKI work—which requires patience, precision, and problem-solving.
This program is intentionally designed to reflect how PKI responsibility grows in real organizations. Participants who succeed are those willing to learn progressively, apply concepts in practice, and develop confidence over time.
Program Commitment & Expectations
This cohort is designed to mirror how PKI work is learned and applied in real enterprise environments. Success requires consistent engagement, applied effort, and a willingness to work through complex systems over time.
Program Commitment at a Glance
Program Length: 6 months (single continuous cohort)
Phases: Foundations → Operations → Engineering & Architecture
Format: Instructor-led sessions, guided labs, and applied scenarios
Learning Style: Progressive, hands-on, real-world focused
Time & Participation Expectations
Participants are expected to:
Attend scheduled cohort sessions (live or guided)
Complete hands-on labs tied to each phase
Review technical material between sessions
Apply concepts incrementally as complexity increases
Participate in discussions, walkthroughs, and guided reviews
This is not a passive program. Learning happens through application, iteration, and feedback.
Hands-On & Applied Learning
Accountability & Progression
What This Program Does Not Promise
Throughout the cohort, participants will:
Work with PKI concepts in safe, guided lab environments
Practice issuing, managing, and troubleshooting certificates
Analyze trust models, failures, and operational risks
Progress from understanding concepts → supporting systems → designing architectures
Labs are designed to build confidence without risking production environments.
This program emphasizes readiness over completion.
Progress is measured by:
Technical understanding
Ability to explain PKI concepts clearly
Confidence navigating operational scenarios
Growth in architectural and decision-making thinking
Advancement through the phases reflects skill development—not just time spent.
To set clear expectations:
This is not a certification bootcamp
This does not guarantee job placement
This is not a self-paced video library
This does not shortcut real PKI experience
Instead, the program provides structured exposure, guided practice, and career-aligned readiness.
Participants who commit fully leave the program with practical PKI experience, clearer career alignment, and the confidence to operate, support, and design PKI systems in real-world environments.
Apply to the PKI Career Pathway Cohort
-
How Enrollment Works
This cohort is intentionally small and guided to ensure depth of learning and meaningful progression.
Participants move through a structured intake process to ensure alignment and readiness.
The process includes:
Application Submission
Share your background, goals, and current experience level.Alignment Review
Applications are reviewed to ensure the cohort is the right fit.Enrollment Confirmation
Accepted participants receive cohort details, schedule, and onboarding instructions.This process ensures every participant enters prepared to fully engage in the program.
-
PKI Career Pathway Cohort
Duration: 6 months
Format: Guided cohort + labs
Focus: PKI Foundations → Operations → Engineering & Architecture
Applications are reviewed on a rolling basis. Cohort size is limited.
Pricing, payment options, and FAQs are available on the enrollment page.
Frequently Asked Questions
-
No. This is a hands-on, guided training cohort focused on building real PKI capability and readiness. The emphasis is on applied experience, not test prep.
-
No prior PKI experience is required. The program begins with foundations and progresses intentionally through operations and engineering.
A general understanding of IT or security concepts is helpful. -
This program uses a hybrid model.
Participants complete self-paced technical material and labs, supported by guided sessions, structured milestones, and cohort checkpoints.
Progression is intentional and sequenced — not ad hoc or fully independent. -
Participants should plan for consistent weekly engagement across learning modules, labs, and cohort activities.
The program is designed for professionals who can commit to steady, long-term skill development. -
No. This program does not guarantee job placement.
It prepares participants with the skills, confidence, and applied experience needed to pursue PKI-focused roles and advance responsibly. -
Pricing and enrollment are managed through the enrollment platform after acceptance.
-
Applications are reviewed for alignment.
Accepted participants receive onboarding instructions, platform access, and cohort start details.
